Published May 2026
Bootstrapping Comper with the Rust board

Author
Jouke Waleson
CTO and Co-Founder
A magical achievement for any new language is when you've bootstrapped the compiler. The language is mature enough that you can use it to now build the compiler with itself.
Comper isn't a compiler, so this magical moment isn't available to us. However, we are using Comper for our development process, now. As we've optimized for performance we started building in Rust, and many of our dependencies are on our public Rust OSS board, and we now often use it to choose between two similar dependencies: we look at their velocity, amount of contributors and security posture.
Normally this isn't trivial. You need to clone the repo, run some git analysis commands (like the HN post “Git commands I run before reading any code”), and run something like Google's OSV Scanner to find security issues.
With Comper, we're collecting these stats continuously. Here's how we recently used it when we noticed a lack of activity in one of the main libraries we depended on. (No name, we're not into shaming OSS projects.) We decided to take a closer look.
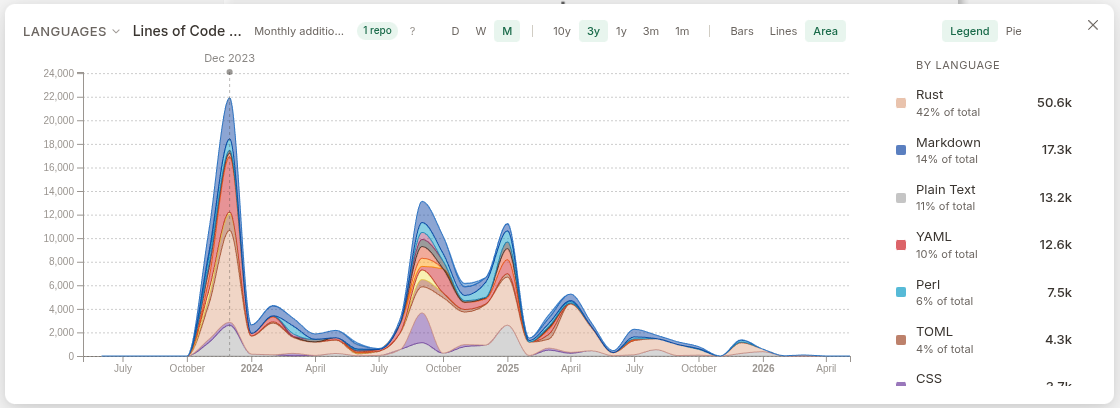
Here we see the amount of changes in LoC per week over the last 3 years. The project is clearly not moving forward, and we did actually need it to implement some of the pull requests we had made to it. We bit the bullet and switched to a different framework.
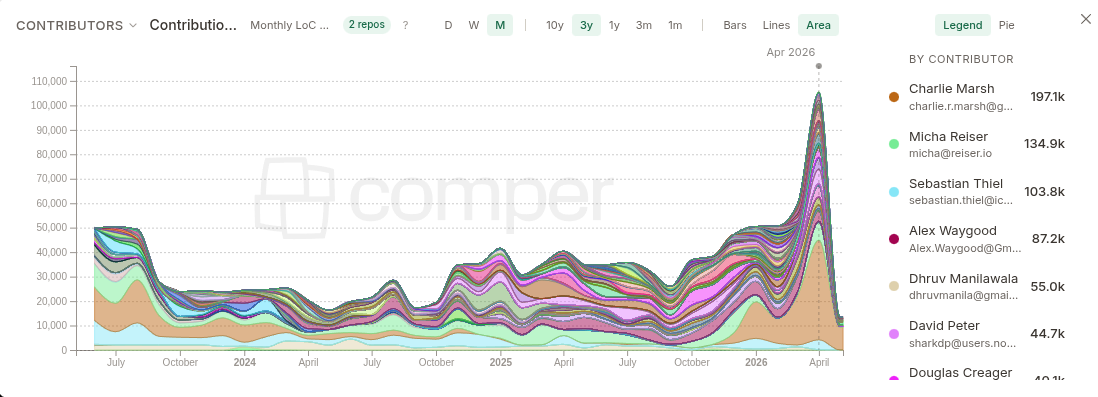
Last year we also decided to move from libgit2 to gitoxide, because we needed more parallelism and speed, and gitoxide is a super cool project. We have built our entire forward git blame engine on top of it.
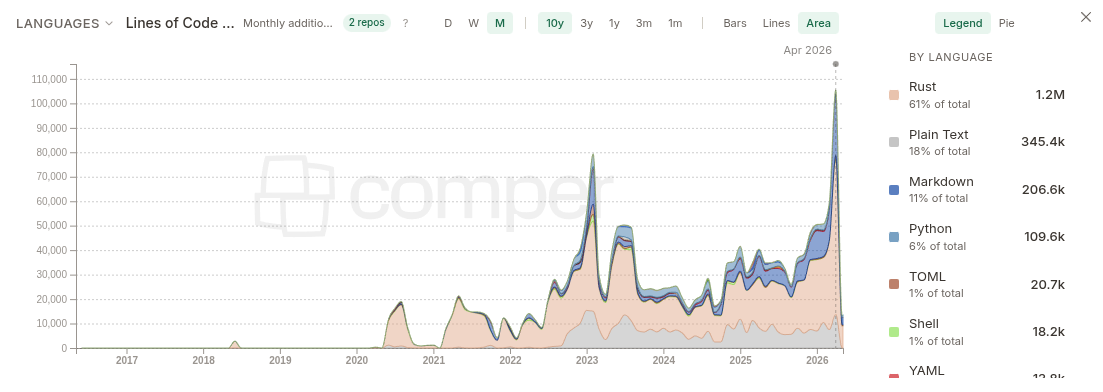
Looking at the velocity and amount of different contributors in the project is awesome. It's clear that gitoxide is gaining a lot of momentum.
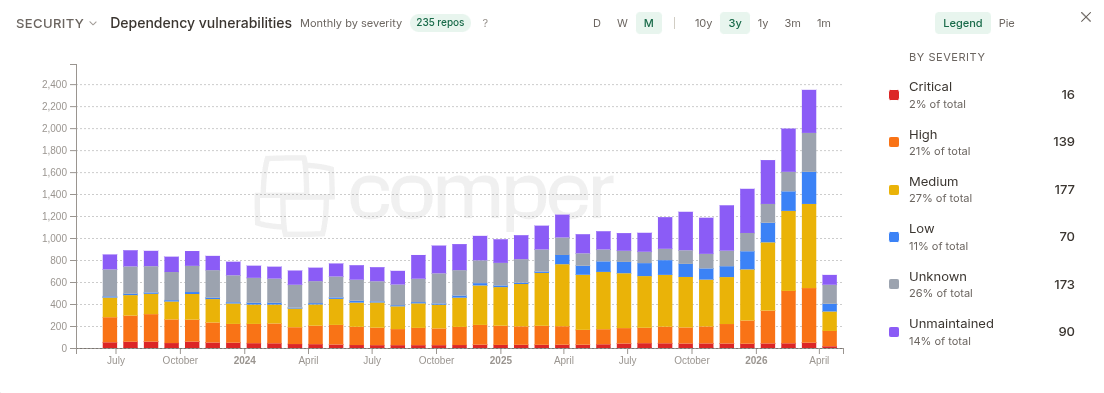
However, it does have some CVEs in its dependencies which hopefully will be picked up soon.
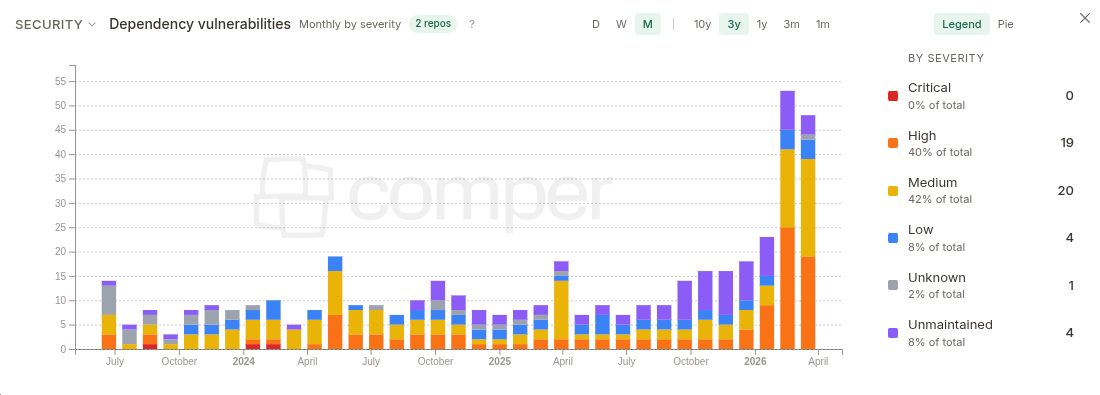
When we zoom out over the entire landscape though, we see an increase in the overall vulnerabilities. We're not sure, but suspect it's due to agents finding more and more security problems in OSS projects.
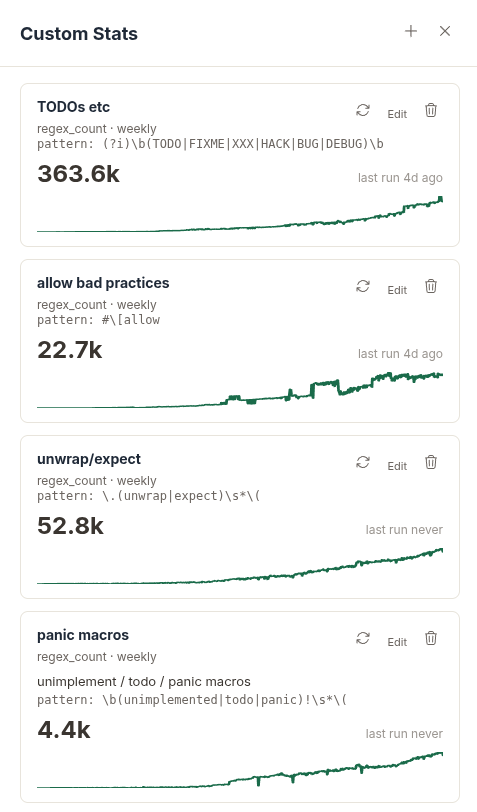
Lastly we also started tracking code smells. These are custom stats with a small regex engine that you can run on all your repos. Still in beta, but helps us keep our code clean.
Found anything interesting yourself? Whether you are weighing two similar crates, watching a dependency go quiet, or trying to get one shared picture of risk across repos, the same kinds of signals we rely on internally show up on the public boards we ship with Comper. If you have not seen it yet, read our launch post on the Rust OSS board and GitShuffle. It walks through what we measure, why we started with Rust, and how we think about dark code at scale. When something on your board surprises you, good or bad, we would love to hear about it.
Ready to see how Comper can strengthen your software?
Jump straight in or talk to the team.
Questions or stories of your own? Email us at [email protected].